This post features three primary parts. Firstly, in this post I will lay out the new Google censorship guidelines utilizing the Ars Technica article that introduced the guidelines to the public in early summer 2017. Secondly, I will provide videos from a number of western political channels where the channel personality explains how censorship and demonetization is affecting their viewcounts, income and ability to be seen and heard expressing their political viewpoints. Thirdly, at the conclusion of this post I will demonstrate that terrorist channels and real pro-Nazi You Tube channels around the world are being given a completely free pass to expose their propaganda by You Tube (Google) as of August 4th, 2017 (date of this post).
______________________________________
Linked directly below is the article that explains the new Google censorship guidelines. (Note that they state they are going after “extremist and hate-filled content”.)
Excerpt:
Google knows there’s a lot of extremist and hate-filled content on YouTube, and the company is now doing more to stop those videos from gaining traction. In a blog post yesterday, Google laid out four new steps it will take to work against extremist videos on YouTube, and most of those steps expand on current systems the company has in place to identify, flag, demonetize, and essentially hide hate-filled videos.
The most nebulous of the four measures is the third listed in the blog post, which states that Google and YouTube will take a “tougher stance” on videos that don’t clearly violate YouTube’s policies. The blog post describes these videos as containing “inflammatory religious or supremacist content”; those videos may not fall under YouTube’s definition of hate speech, but they’ll now be targeted in a similar way.
YouTube clarifies “hate speech” definition and which videos won’t be monetized
“In the future these will appear behind an interstitial warning and they will not be monetized, recommended or eligible for comments or user endorsements,” Kent Walker, general counsel for Google, wrote in the blog post. “That means these videos will have less engagement and be harder to find. We think this strikes the right balance between free expression and access to information without promoting extremely offensive viewpoints.”
The link directly below is to the official Google Blog post on the censorship guidelines mentioned in the Ars Technica article above:
Google – Four steps we’re taking today to fight terrorism online – June 18, 2017
__________________________________________________
Featured below are a number of channels of various political stylings that Google has begun censoring and demonetizing under the new censorship guidelines. Each channel personality explains in each video how the Google censorship guidelines are personally affecting them and how the censorship will effect the public as a whole. Between each video will be additional portions of the Ars Technica article that reveal the new censorship guidelines in their entirety. At the conclusion of this post I will provide links and screenshots from actual terrorist and pro-Nazi channels as proof that only western political commentary that exposes war crimes, propaganda and the Deep State agenda is actually being censored by Google, while real terrorists and real murderous Nazi groups are clearly being given a free pass by Google as of August 4, 2017.
Caveat: My use of these channels to make a point does not necessarily mean I endorse their viewpoints. I am simply against censorship in any form. People who read Clarity of Signal regularly likely realize that I lean progressive ideologically, however, I am not attached to any particular political party and instead now simply focus on exposing warcrimes, false flags and corruption amongst the government and global elite. I have had a good many people from all political affiliations help me attain info for posts at the site. Each one of these videos provides a good synopsis of what is going on regarding You Tube/Google censorship.
Support the WSWS’s fight against Google censorship.
Censored political discussion channel 1-StyxHexHammer
Censored political discussion channel 2 – Lionel Nation
Ars Technica excerpt 2-
How are Google and YouTube taking this tougher stance against gray-area videos? The other measures outlined in the blog post explain further. Google will increase the amount of technology used to identify extremist videos, meaning the company will expand the sophistication of its machine learning technology that can tell the difference between extremist content and non-extremist content.
FURTHER READING
Big US companies pull YouTube ads after extremist content sparks uncertainty
This is particularly important for any YouTube channel that discusses news and current events, because until now, those channels have been heavily demonetized because they talk about sensitive, violent, and extremist events while reporting the news. The blog post states that the company will now use “advanced machine learning research to train new ‘content classifiers’ to help us more quickly identify and remove extremist and terrorism-related content.”
Google will also increase YouTube Trusted Flagger networking, which is a group of companies and individuals that have the power to flag videos with offensive content. Google will add 50 expert NGOs to the existing 63 organizations in the program and support them with additional grants. Lumped into the Trusted Flagger program is the YouTube Heroes program, which initially raised the eyebrows of many creators as it let any YouTube user apply to be someone who flags offensive content on the platform. Some creators have expressed concern that user biases could cause some of their videos to be unnecessarily flagged or demonetized. However, creators can initiate a review process for any demonetized video if they think it doesn’t contain offensive material or content that violates YouTube policies.
Censored political discussion channel 3 – Paul Joseph Watson
Censored political discussion channel 4 – Mark Dice –
Ars Technica article excerpt 3 –
The final measure from Google is an expansion of its counter-radicalization efforts on YouTube. This is arguably the most active and purposeful new step out of the four, as it expands on the “redirect method” originally developed by Google Ideas, a think tank now known as Jigsaw. Born last year, the “redirect method” essentially uses targeted advertising to guide potential ISIS recruits away from radicalization videos. Ads are placed next to search results for keywords and phrases that have been deemed ISIS-related, and when clicked, those ads bring the user to YouTube channels consisting of videos debunking ISIS teachings. The theory is that potential ISIS recruits will be dissuaded from learning about or joining the terrorist organization after watching those videos.
The “redirect method” is a new initiative that’s barely one year old, but Google believes it has had a positive effect. While Google can’t quantify how many potential ISIS recruits have abandoned their terrorism-related research, the company does claim “potential recruits have clicked through on the ads at an unusually high rate, and watched over half a million minutes of video content.”
Internet companies are under immense pressure to do something about hate speech on their platforms. Facebook is taking a similar approach to Google, pledging to use AI and more human moderators to eliminate extremist content on its website, while Twitter unabashedly suspends accounts that promote terrorism. Google’s new measures are undoubtedly another response to the ad exodus that occurred earlier this year, in which many companies pulled advertising from YouTube after ads were found running over hate-filled videos. Until now, YouTube has focused on giving advertisers more tools to control where their ads appear and more clearly defining what “extremist” and “offensive” content means for their creators. But there is no longer any ambiguity on what Google and YouTube will be doing going forward—they will not only come down hard on offensive content, but they will also do more to ensure extremist content can’t be easily found on YouTube.
Censored political discussion channel 5 – David Seaman –
Internationally renowned investigative reporter Robert Parry of Consortium News and Iran-Contra fame covers “The Dawn of an Orwellian Future”, and specifically, the Google censorship of the World Socialist Website shown in the video up above.
Consortium News – The Dawn of an Orwellian Future July 28, 2017
Excerpt:
A report by the World Socialist Web Site found that “in the three months since Internet monopoly Google announced plans to keep users from accessing ‘fake news,’ the global traffic rankings of a broad range of left-wing, progressive, anti-war and democratic rights organizations have fallen significantly.” Google’s strategy is to downgrade search results for targeted Web sites based on a supposed desire to limit reader access to “low-quality” information, but the targets reportedly include some of the highest-quality alternative news sites on the Internet, such as – according to the report – Consortiumnews.com.
Google sponsors the First Draft Coalition, which was created to counter alleged “fake news” and consists of mainstream news outlets, including the Times and The Washington Post, as well as establishment-approved Web sites, such as Bellingcat, which has a close association with the anti-Russia and pro-NATO Atlantic Council. This creation of a modern-day Ministry of Truth occurred under the cover of a mainstream-driven hysteria about “fake news” and “Russian propaganda” in the wake of Donald Trump’s election.
Last Thanksgiving Day, the Post ran a front-page article citing accusations from an anonymous Web site, PropOrNot, that identified 200 Web sites — including such Internet stalwarts as Truthdig, Counterpunch and Consortiumnews — as purveyors of “Russian propaganda.” Apparently, PropOrNot’s standard was to smear any news outlet that questioned the State Department’s Official Narrative on the Ukraine crisis or some other global hot spot, but the Post didn’t offer any actual specifics of what these Web sites had done to earn their place on a McCarthyistic blacklist.
An Orwellian Future
In early May 2017, the Times chimed in with a laudatory article about how sophisticated algorithms could purge the Internet of alleged “fake news” or what the mainstream media deems to be “misinformation.” Big Brother poster illustrating George Orwell’s novel about modern propaganda, 1984. As I wrote at the time, “you don’t need a huge amount of imagination to see how this combination of mainstream groupthink and artificial intelligence could create an Orwellian future in which only one side of a story gets told and the other side simply disappears from view.”
End Excerpt – (More at link above)
Link to World Socialist Website Report –
1st excerpt:
In the three months since Internet monopoly Google announced plans to keep users from accessing “fake news,” the global traffic rankings of a broad range of left-wing, progressive, anti-war and democratic rights organizations have fallen significantly. On April 25, 2017, Google announced that it had implemented changes to its search service to make it harder for users to access what it called “low-quality” information such as “conspiracy theories” and “fake news.” The company said in a blog post that the central purpose of the change to its search algorithm was to give the search giant greater control in identifying content deemed objectionable by its guidelines. Google declared that it had “improved our evaluation methods and made algorithmic updates” in order “to surface more authoritative content.”
Google continued, “Last month, we updated our Search Quality Rater Guidelines to provide more detailed examples of low-quality webpages for raters to appropriately flag.” These moderators are instructed to flag “upsetting user experiences,” including pages that present “conspiracy theories,” unless “the query clearly indicates the user is seeking an alternative viewpoint.” The World Socialist Web Site has been targeted by Google’s new “evaluation methods.” While in April 2017, 422,460 visits to the WSWS originated from Google searches, the figure has dropped to an estimated 120,000 this month, a fall of more than 70 percent. Even when using search terms such as “socialist” and “socialism,” readers have informed us that they find it increasingly difficult to locate the World Socialist Web Site in Google searches.

According to Google’s webmaster tools service, the number of searches resulting in users seeing content from the World Socialist Web Site (that is, a WSWS article appeared in a Google search) fell from 467,890 a day to 138,275 over the past three months. The average position of articles in searches, meanwhile, fell from 15.9 to 37.2 over the same period. David North, chairperson of the International Editorial Board of the WSWS, stated that Google is engaged in political censorship. “The World Socialist Web Site has been in existence for nearly 20 years,” he said, “and it has developed a large international audience. During this past spring, the number of individual visits to the WSWS each month exceeded 900,000. “While a significant percentage of our readers enter the WSWS directly, many web users access the site through search engines, of which Google is the most widely used. There is no innocent explanation for the extraordinarily sharp fall in readers, virtually overnight, coming from Google searches.
“Google’s claim that it is protecting readers from ‘fake news’ is a politically motivated lie. Google, a massive monopoly, with the closest ties to the state and intelligence agencies, is blocking access to the WSWS and other left and progressive web sites through a system of rigged searches.” In the three months since Google implemented the changes to its search engine, fewer people have accessed left-wing and anti-war news sites. Based on information available on Alexa analytics, other sites that have experienced sharp drops in ranking include WikiLeaks, Alternet, Counterpunch, Global Research, Consortium News and Truthout. Even prominent democratic rights groups such as the American Civil Liberties Union and Amnesty International appear to have been hit.
More at link above…..
Graphic from above WSWS article showing declining traffic rates for site that expose warcrimes, global corruption and Deep State activities.

Now that we’ve taken a look at what Google is censoring, demonetizing and driving down in the algorithms of its search engine, let’s look at what is not currently being censored by Google.
As many Clarity of Signal readers are likely aware, this site has been one of the leading sites exposing terrorists in Syria and Libya, as well as Nazis in Ukraine. During the past 3 years I have compiled a massive amount of photo and video evidence in a number of posts clearly showing the murderous organizations that conduct terrorism while receiving funding from western governments and help from corrupt media outlets. This site clearly exposes the White Helmets terrorist ruse that western governments and media have foisted on the citizenry that they are supposed to be representing and working for. My work exposing the murderous, fascist Nazi battalions in Ukraine is extensive and includes dozens of their own videos from their own Azov You Tube channel.
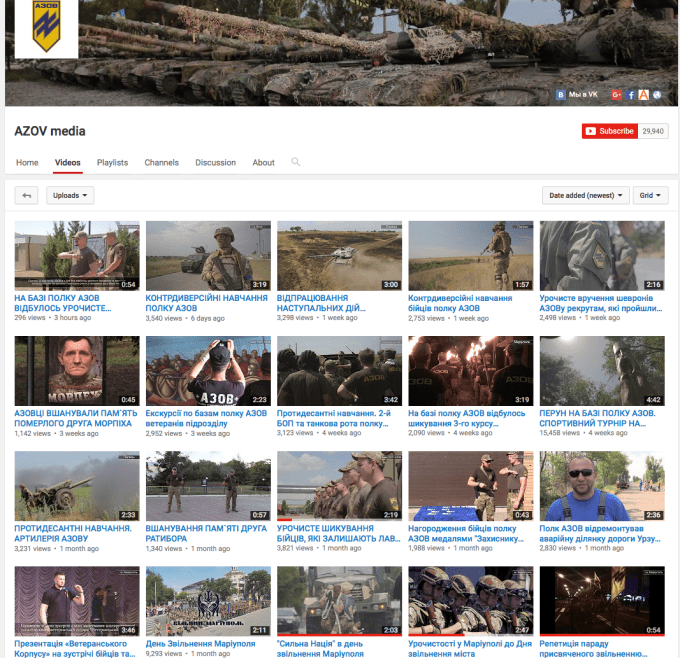
Those Ukrainian Nazis are still freely posting videos up on You Tube as of August 4th, 2017, and have been given a free pass by Google, even though Human Rights Watch and Amnesty International have implicated them in war crimes against innocent civilians. This is the Azov battalions You Tube channel main page…… they are real Nazis:
https://www.youtube.com/channel/UCewl92lzIMDO8QiAYOQ2d8w/videos
Screen shot from August 4th, 2017
Link to Amnesty International and HRW reports on the warcrimes of the Aidar and Azov battalions:
Excerpt from Item 2 –
58. OHCHR documented allegations of unidentified armed men detaining people living near the conflict zone due to their alleged affiliation with armed groups. They complained about being subjected to ill-treatment and torture in order to extract confessions that they assisted armed groups. Following their confessions, they were taken to SBU premises and officially charged. OHCHR has consistently observed that the SBU fails to inquire into the condition of detainees and the circumstances of their capture. This pattern of conduct suggests that SBU investigators may either be involved in certain cases of arbitrary detention, or fail to act to prosecute perpetrators.
59. A resident of Mariupol was detained by three servicemen of the ‘Azov’ battalion on 28 January 2015 for supporting the ‘Donetsk people’s republic’. He was taken to the basement of Athletic School No. 61 in Mariupol, where he was held until 6 February 2015. He was continuously interrogated and tortured. He complained about being handcuffed to a metal rod and left hanging on it, he was reportedly tortured with electricity, gas mask and subjected to waterboarding and he was also beaten in his genitals. As a result he confessed about sharing information with the armed groups about the locations of the Government checkpoints. Only on 7 February, he was taken to the Mariupol SBU, where he was officially detained.
60. Allegations of torture and ill-treatment are rarely investigated. There are few prospects for accountability for abuses perpetrated by members of law enforcement agencies. In some cases, attempts by victims of torture to complain to judges in the course of a hearing have been met with inaction and callousness, with judges frequently ignoring or dismissing complaints, revealing the judiciary’s lack of impartiality.
____________________________________________________
This is the You Tube channel of terrorist and al- Nusra Front information disseminator Bilal Abdul Kareem who promotes the leader of al-Nusra Front (al-Qaeda in Syria) Abdullah al-Muhaysini. He works for On The Ground News (a pro-terrorist You Tube propaganda channel). In this video which is still up on his pro-terrorist OGN You Tube channel on August 4th, 2017, he showers praise upon Abdullah al-Muhaysini, the leader of al-Nusra Front. Keep in mind that it took less than 30 seconds for me to find this video, yet Googles ‘impressive’ new algorithms that weed out ‘extremist content’ have completely overlooked this material and given it a free pass. This is a terrorist that murders people by blowing them up with explosives, shooting them in the face at point blank range and cutting off human heads, yet he completely receives a free pass from Google and You Tube as of August 4th, 2017. A video channel that openly promotes terrorism and the leader of al-Qaeda in Syria is completely, glaringly unaffected by Googles new censorship guidelines which appear to affect only content that deals with exposing western support for terrorist groups.
In case the video above is removed after this CoS article is published, here are some screen shots from the video:
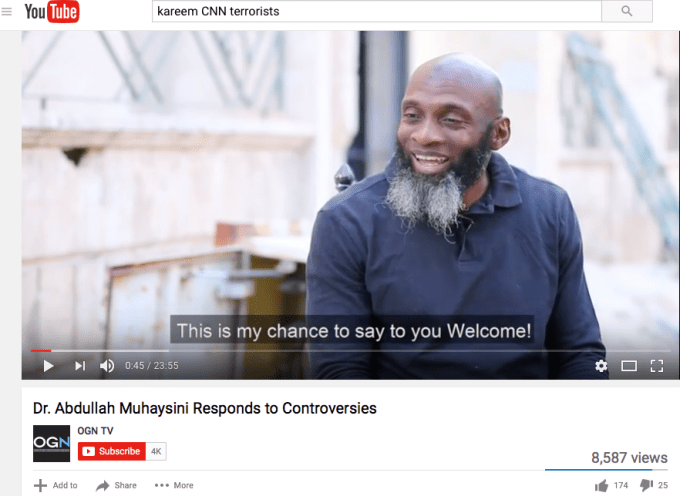
Note that I left the search terms up there for people to see in the screenshot. Why did I add CNN to the search terms you may wonder? Well, its because CNN actually gave an award to this mouthpiece for terrorists. That fact is exposed in the Tapestry of Terror video I put together linked below. CNN and Amnesty International actually gave that terrorist mouthpiece an award for his pro terrorist propaganda.
Link here: Tapestry of Terror (Highly Graphic) – White Helmets Exposed As FSA Terrorists Linked With ISIS
2nd screenshot:

3rd:

Link proving these terrorists propaganda networks/You Tube channels should have been shut down over 10 months ago. Thus, proving Googles new censorship agenda is not focused on stopping terrorism, and is instead, focused on stifling political dissent of concerned citizens and alternative media outlets who oppose US and EU (western) nefarious actions related to support for terrorists and fascist regimes, as well as dissent surrounding the controversy around the 2016 US election, blame Russia narrative and Wikileaks revelations.
Treasury Designates Key Al-Nusrah Front Leaders -Abdallah Muhammad Bin-Sulayman al-Muhaysini
Screenshot and link proving that CNN and Amnesty International actually gave a TV Trophy Award to the terrorist Bilal Abdul Kareem
TELEVISION TROPHY – INTERNATIONAL JURY AWARDED BY AMNESTY INTERNATIONAL

This third channel belongs to Hadi Abadallah whose You Tube channel allows him the opportunity to promote the White Helmets terrorists in Syria as well as numerous FSA terrorist groups, including the Nour al-Zinki child beheaders. Evidence proving such can be found among my other Clarity of Signal posts related to Syrian ruses conducted in collaboration with the US and EU governments and corrupt mainstream media outlets.
https://www.youtube.com/channel/UCo_dRDd4m7fgCNdfwLAPKMA/videos
Note that You Tube/Google could just as easily track down this terrorists propaganda channel and shut him and it down. I have personally been exposing that him as a terrorist who conducts false flags alongside the White Helmets, who are also terrorists, for the past year. Instead of shutting them down, Google has, as of August 4th, 2017, decided to allow him a free pass, as has the US and western governments who support his nefarious and murderous cause.
In the below linked post I expose the terrorist Hadi Abadallah fully for all to see:
Lastly, these are the current accounts of Abdullah al-Muhaysini himself. He has multiple accounts. They are not censored or blocked by You Tube/Google. They are easy to access as of August 4th, 2017. Screen shots are included in case these accounts are removed after this CoS post goes live.
1st account established on May 12, 2017 : https://www.youtube.com/channel/UCIQUPhL43Ln74oq3aDYzVHg
Screenshot: 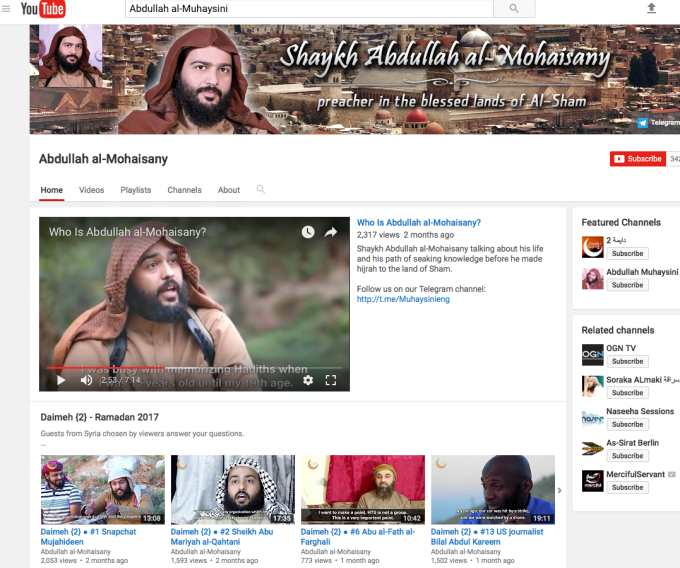
2nd account established on October 28th, 2016 : https://www.youtube.com/channel/UC7aa3C_TOaOEkgiu0Rp3bVQ
Screenshot 1:

Screenshot 2:

Sample of basic search results under the name of the al-Qaeda leader in Syria proves he and his followers are not censored and are free to post as they like, with no censorship from Google/You Tube. These screenshots prove that the censorship being conducted by You Tube and Google is not being carried out for the purposes they specify in their new censorship guidelines due to the fact that well known terrorists, including the leader of al-Qaeda in Syria still have their channels up and fully operational.

Additional You Tube political personalities discuss You Tube demonetization of their accounts in 2016 when You Tube first introduced the demonetization of political content that doesn’t match the selected corporate news criteria-
Jimmy Dore show –
TruthStream Media –
Sane Progressive explains what all this censorship and control is really all about…
Link to additional Clarity of Signal posts on Google, You Tube and Facebook censorship and demonetization:
To preview Google’s AI Web Filtering Algorithm and see for yourself which terms are deemed acceptable or toxic, I highly recommend the following link:
Dregs of the Future – Preview Google’s AI Web Filtering Algorithm–censorship
To see how Goole got its start as a Deep State tool, check out this link:
How the CIA made Google Inside the secret network behind mass surveillance, endless war, and Skynet—Pt 1
Why Google made the NSA Inside the secret network behind mass surveillance, endless war, and Skynet—Pt 2
Recommended reading:
YouTube Begins Purging Alternative Media as the Deep State Marches Toward WW3
Recommendations for concerned citizens tired of the censorship:
VidMe – https://vid.me
Steemit Video: https://steemit.com/steemq/@furion/steemq-a-decentralized-video-platform-for-steem
https://steemit.com/steemq/@furion/teaser-soon-you-will-be-able-to-publish-videos-on-steem
You can now publish videos to your own Steemit blog on Viewly
RU Tube – https://rutube.ru (Caveat – site is not in English, but someone putting together a quick tutorial on how to post using Russian/English screenshots could make this a very valuable resource).
For a search engine with a better selection of search results and no tracking of your online activity – https://duckduckgo.com/


